Trap Sack Nude Leak: The Shocking Reality Behind The Trend!
What happens when digital privacy meets viral internet trends? In today's interconnected world, the phenomenon of trap sack nude leaks represents a disturbing intersection of technology, privacy violations, and social media culture. This article explores the complex landscape of digital exploitation, from seemingly innocent viral challenges to sophisticated malware schemes that compromise personal privacy.
The Evolution of Digital Exploitation: Understanding "Trap Sack"
To understand what a trap sack really is, you have to look at the trap itself—the physical and metaphorical space where illegal commerce happens—and how that vocabulary has been hijacked by lifestyle brands and internet memes. The term "trap sack" has evolved from street slang into a broader cultural phenomenon that encompasses various forms of digital deception and exploitation.
In youth culture today, the concept has taken on new meaning, representing the digital equivalent of a physical trap where unsuspecting users become victims of privacy violations. This linguistic evolution reflects how quickly internet terminology can shift from niche communities to mainstream awareness, often carrying dangerous implications along the way.
- Heavy Cream Leak What Theyre Hiding From You Will Change Cooking Forever
- Forbidden Sewing Hack So Addictive Its Like Porn Hem Dress Pants In Under 5 Minutes
The significance of trap sack in contemporary youth culture extends beyond mere vocabulary. It represents a fundamental shift in how young people perceive digital spaces—areas that can be simultaneously entertaining and dangerous, where the line between harmless content and exploitation is increasingly blurred.
The Anatomy of Viral Deception: TikTok's "Invisible Body" Challenge
TikTok's latest trend is the "invisible body" challenge, in which users post seemingly nude videos of themselves. This viral phenomenon has captivated millions of viewers while raising serious questions about consent, privacy, and the platform's responsibility in moderating harmful content.
The challenge operates on a simple premise: users create videos that appear to show nude bodies, but through clever camera angles, strategic positioning, or digital effects, the actual nudity remains hidden or implied. This creates a tantalizing effect that drives engagement while technically staying within the platform's content guidelines.
- The Truth About Epsteins Death Secret Files Leaked Show Hes Alive And Kicking
- Leaked Nude Photos Reveal Canadian Tie To Epsteins Trafficking Ring
However, the trend has spawned numerous variations, some of which are far more concerning. One of the most prevalent versions hides uncensored images from the Wisconsin volleyball team leak in the show, demonstrating how viral challenges can become vehicles for distributing non-consensual intimate imagery.
Experts say the trend is unique and highlights an unknown vulnerability in TikTok. The platform's algorithm, designed to promote engaging content, inadvertently amplifies these trends without fully understanding their implications. This creates a perfect storm where harmful content can spread rapidly before moderation teams can respond.
Malware Distribution: The Hidden Danger Behind "Free Content"
Thousands of users have downloaded malware in hopes of seeing some skin, revealing a disturbing pattern of digital exploitation that preys on human curiosity and desire. Cybercriminals have recognized the appeal of intimate content and weaponized it to distribute malicious software.
These malware schemes typically operate through fake websites, compromised social media accounts, or phishing emails that promise access to exclusive nude content. Once users click through, they're prompted to download files that appear to be images or videos but are actually sophisticated malware designed to steal personal information, encrypt files for ransom, or turn devices into part of a botnet.
The scale of this problem is staggering. Security researchers have documented malware campaigns that specifically target individuals searching for leaked intimate content, with infection rates significantly higher than general malware distribution campaigns. This demonstrates how the promise of forbidden content can override normal security caution.
The economic model behind these schemes is equally troubling. Cybercriminals often operate in organized networks, with different groups specializing in malware creation, distribution, and monetization. The profits from successful infections can fund more sophisticated campaigns, creating a self-perpetuating cycle of exploitation.
The Digital Privacy Crisis: Understanding Nude Leaks
In the digital age, where privacy and personal boundaries are increasingly tested, the phenomenon of nude leaks has emerged as a significant concern. This crisis extends far beyond individual cases, representing a fundamental breakdown in how society values digital privacy and consent.
The causes of nude leaks are multifaceted. Technical vulnerabilities in cloud storage services, social engineering attacks that trick users into revealing passwords, and the simple act of sharing intimate content with untrustworthy partners all contribute to the problem. Additionally, the normalization of sharing intimate content has created an environment where privacy breaches are often treated as entertainment rather than violations.
The consequences extend far beyond the initial exposure. Victims of nude leaks often experience severe psychological trauma, professional damage, and social isolation. The permanent nature of digital content means that once leaked, intimate images can resurface years later, continuing to cause harm long after the initial incident.
This article delves into the complex world of nude leaks, exploring the causes, consequences, and potential solutions to this digital crisis. Understanding the full scope of the problem is essential for developing effective responses at both individual and societal levels.
The Psychology of Online Exploitation: Understanding Audience Behavior
Emo trap porn has cultivated a dedicated audience that goes beyond the typical demographics associated with adult entertainment. While it's difficult to pinpoint an exact profile due to the anonymous nature of online viewing, certain trends have emerged that offer valuable insights.
The audience for this content often includes younger viewers who are drawn to the aesthetic and cultural elements rather than purely sexual content. This demographic tends to be more digitally native, spending significant time on social media platforms and being more susceptible to viral trends and challenges.
Research suggests that many viewers don't initially seek out exploitative content but rather stumble upon it through algorithmic recommendations or peer sharing. This passive consumption model makes it difficult to address the problem through traditional content moderation approaches, as the demand is often created by the platform's own recommendation systems.
The psychological factors driving consumption include curiosity, the desire for forbidden content, and the social validation that comes from sharing trending material. Understanding these motivations is crucial for developing effective interventions that address the root causes rather than just the symptoms of digital exploitation.
Real-World Consequences: Beyond the Digital Realm
Today brings yet another example of how digital exploitation has real-world consequences. The case of Stephanie Minter, allegedly murdered by an individual with more than 30 previous arrests, highlights how online behaviors and offline crimes intersect in complex ways.
While this particular case involves immigration enforcement debates, it serves as a reminder that the individuals behind digital exploitation often have extensive criminal histories that extend beyond the virtual world. The same lack of respect for boundaries and consent that enables nude leaks can manifest in violent crimes.
The connection between online exploitation and real-world harm is becoming increasingly clear. Studies have shown correlations between consumption of non-consensual intimate imagery and increased likelihood of committing sexual offenses. This suggests that addressing digital exploitation could have broader benefits for public safety.
The refusal of some media outlets to report on cases involving illegal immigrants and violent crimes creates information gaps that can prevent effective policy responses. This selective reporting can also contribute to the normalization of certain types of exploitation while demonizing others, creating an inconsistent approach to digital privacy violations.
Platform Responsibility and Technical Vulnerabilities
Experts say the trend is unique and highlights an unknown vulnerability in TikTok. This statement encapsulates a broader issue affecting all social media platforms: the challenge of balancing user engagement with content safety.
The algorithmic nature of content recommendation systems means that platforms often amplify harmful trends without fully understanding their implications. By the time moderation teams can respond, millions of users may have already been exposed to exploitative content or malware.
Technical vulnerabilities extend beyond content moderation. The infrastructure that enables viral content sharing can also facilitate the rapid spread of malware and non-consensual imagery. Cloud storage services, messaging apps, and social media platforms all contain potential weaknesses that can be exploited by bad actors.
Platform responsibility extends to the development of more sophisticated content analysis tools, improved reporting mechanisms, and transparent communication with users about privacy risks. However, the pace of technological change often outstrips the ability of platforms to implement effective safeguards.
The Cultural Context: Fashion, Media, and Digital Exploitation
The latest fashion news, beauty coverage, celebrity style, fashion week updates, culture reviews, and videos on Vogue.com represent the mainstream media's approach to digital content. However, even respected publications can inadvertently contribute to the normalization of exploitative content through their coverage choices.
The intersection of fashion, celebrity culture, and digital exploitation creates complex ethical challenges. When mainstream media outlets feature celebrities who have experienced nude leaks or participate in controversial viral challenges, they can unintentionally legitimize harmful content.
The professionalization of digital content creation has created new career opportunities but also new vulnerabilities. Influencers and content creators often push boundaries to maintain engagement, sometimes crossing into exploitative territory without fully understanding the implications.
The advertising solutions across trusted brands highlight how the economic model of digital media can incentivize controversial content. Brands seeking to reach younger audiences may inadvertently support platforms or creators who distribute exploitative material.
Professional Networks and Digital Exploitation
Explore top LinkedIn content from members on a range of professional topics reveals how even professional networking platforms are not immune to digital exploitation. While LinkedIn maintains stricter content guidelines than social media platforms, the professional context can make exploitation more damaging.
The career opportunities, leadership, and advertising solutions across trusted brands section of professional platforms can be compromised by individuals using professional contexts to distribute exploitative content. This creates unique challenges for moderation teams who must balance professional networking with content safety.
The digital literacy gap between different professional demographics means that older professionals may be more vulnerable to sophisticated exploitation schemes that target their specific interests or career concerns. This creates a need for targeted education and awareness campaigns within professional communities.
Solutions and Prevention Strategies
Addressing the trap sack nude leak phenomenon requires a multi-faceted approach that combines technical solutions, policy changes, and cultural shifts. At the individual level, digital literacy education is crucial for helping users recognize and avoid exploitation attempts.
Technical solutions include improved content moderation tools, better malware detection, and more secure storage options for intimate content. However, technology alone cannot solve the problem, as human behavior and cultural attitudes play significant roles in perpetuating exploitation.
Policy interventions at the platform level include stricter content guidelines, faster response times to reported violations, and transparency about content recommendation algorithms. Legal frameworks need to evolve to address the unique challenges of digital exploitation, including international cooperation to prosecute offenders across borders.
Cultural change requires challenging the normalization of non-consensual intimate imagery and creating social consequences for those who distribute such content. This includes education about consent, privacy rights, and the real-world harm caused by digital exploitation.
The Path Forward: Building a Safer Digital Future
The shocking reality behind trap sack nude leaks represents just one aspect of a broader digital privacy crisis. As technology continues to evolve, new forms of exploitation will emerge, requiring constant vigilance and adaptation from users, platforms, and policymakers.
The key to addressing this challenge lies in understanding the complex interplay between technology, human behavior, and cultural attitudes. By recognizing how viral trends, malware distribution, and platform vulnerabilities intersect, we can develop more effective strategies for protecting digital privacy.
Individual responsibility remains crucial, but it must be supported by institutional changes that make exploitation more difficult and less profitable. This includes everything from improved technical safeguards to cultural shifts that value digital consent and privacy.
The future of digital privacy depends on our collective ability to recognize and respond to emerging threats while maintaining the benefits of digital connectivity. Only by addressing the root causes of exploitation can we create a digital environment that respects personal boundaries and protects vulnerable individuals.
Conclusion
The trap sack nude leak phenomenon represents a complex challenge that sits at the intersection of technology, culture, and human behavior. From viral TikTok challenges to sophisticated malware schemes, the methods of digital exploitation continue to evolve, requiring equally sophisticated responses.
Understanding the full scope of this problem—from the technical vulnerabilities that enable exploitation to the cultural factors that normalize it—is essential for developing effective solutions. This requires collaboration between technology companies, policymakers, educators, and users to create a comprehensive approach to digital privacy protection.
The shocking reality is that digital exploitation affects millions of people across all demographics, creating real-world harm that extends far beyond the initial privacy violation. By recognizing the interconnected nature of these challenges and implementing comprehensive solutions, we can work toward a digital future that respects privacy, values consent, and protects vulnerable individuals from exploitation.
- What This Golden Retriever Chose For His Birthday Will Shock You
- I Pick Clarke Exposed The Nude Photo Scandal That Changed Everything
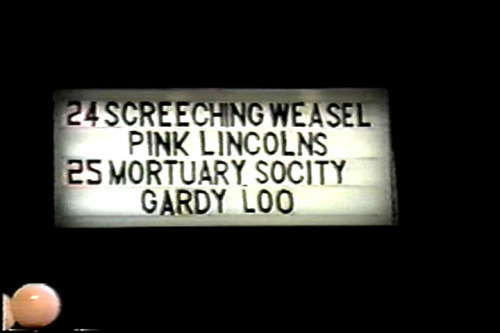
Shocking Reality Concert & Tour History | Concert Archives
Shocking Reality Behind Huxley's Brave New World - Jay Dyer (Half)

Sack Trap | Roblox BEAR Wiki | Fandom