SHOCKING LEAK: June 27th Birthday Secrets Exposed – Nude Photos Inside!
Have you ever wondered what happens when private celebrity moments become public? The digital age has brought us closer to our favorite stars than ever before, but it has also exposed them to unprecedented privacy violations. When intimate photos and videos are leaked, the consequences ripple far beyond the initial shock value, sparking intense debates about privacy, security, and the ethics of consuming such content.
The Dark Side of Celebrity Culture
The entertainment industry has long been plagued by privacy breaches, with countless celebrities falling victim to malicious hacking and unauthorized leaks. From major Hollywood stars to rising talents, no one seems immune to the threat of having their most intimate moments exposed to the world.
From Box Office Stars to Teen Idols
The scope of these leaks is truly staggering, affecting actors and actresses across all levels of fame. Big-budget franchise leads, known for their blockbuster performances, have found themselves in the uncomfortable position of having their private photos circulate online. Similarly, former teen TV stars who grew up in the public eye have faced the additional trauma of having their adult private lives exposed, often at the most vulnerable moments of their careers.
- Trump Just Dropped A Nuclear Bomb Epsteins Sex Files Leaked Nude Photos And Orgies Exposed
- Exclusive Leak Predador De Perereca English Translation Reveals Shocking Nude And Sex Lyrics
These incidents highlight a disturbing trend where the same platforms that help celebrities connect with fans can also become weapons against them. The psychological toll on victims is immeasurable, as they must navigate both the public humiliation and the violation of their most personal boundaries.
The Growing Epidemic of Online Exposure
Dozens of Hollywood celebrities have accidentally exposed themselves online over the years, whether through hacking incidents, cloud storage breaches, or simple human error. The problem has become so widespread that it's no longer a question of if a celebrity will face such a leak, but when and how severe it will be.
The technology that makes our lives more convenient also creates new vulnerabilities. Cloud storage services, while incredibly useful, have become prime targets for hackers seeking compromising material. Social media platforms, designed to foster connection, can quickly become distribution channels for private content without consent.
- What The Housekeeper Saw Epsteins Hidden Orgies And Leaked Porn Scandal Revealed
- Leaked The Funniest Group Chat Names That Accidentally Included Nude And Sex Now Viral
A Comprehensive Look at Celebrity Photo Leaks
This article offers a comprehensive list of famous people with leaked photos, detailing the experiences of various celebrities who had their private moments exposed through hacking incidents. Each case tells a story not just of violation, but of resilience and the ongoing fight for digital privacy rights.
The 2014 iCloud Hack: A Watershed Moment
One of the most notorious incidents in recent memory was the massive 2014 iCloud hacking, which compromised several celebrity accounts simultaneously. This coordinated attack affected dozens of high-profile individuals, with intimate images of her beginning to circulate online almost immediately after the breach.
The scale and sophistication of this hack shocked the world and led to significant changes in how both celebrities and tech companies approach digital security. It became clear that no amount of fame or fortune could protect against determined cybercriminals who exploited weaknesses in cloud storage systems.
Beyond the Headlines: The Human Cost
What many people don't realize is that these leaks have real, lasting consequences for the victims. Beyond the initial shock and embarrassment, celebrities often face career setbacks, relationship problems, and severe mental health challenges. The constant reminder that their most private moments are available for public consumption can be devastating.
The leak didn't go to CNN or other major news outlets, but that didn't stop the images from spreading across the internet like wildfire. This highlights an important distinction: while mainstream media may exercise restraint in publishing such content, the internet has no such filters, and once something is online, it's nearly impossible to completely remove.
Tools and Resources for Content Creators
Chiliradar: A Free Tool for Content Creators
In response to the growing problem of leaked content, various tools have emerged to help both victims and content creators navigate this challenging landscape. Chiliradar is a free tool for content creators to find and track leaked content, providing a way to monitor where private material might be appearing online.
This type of tool represents a double-edged sword in the digital age. While it can help content creators protect their intellectual property and monitor unauthorized distribution of their work, it can also be used to facilitate the very behavior it seeks to combat. The ethical implications of such tools continue to be debated within the industry.
Scanning Leaked OnlyFans and Fansly Content
The rise of subscription-based adult content platforms like OnlyFans and Fansly has created new challenges in the realm of digital privacy. Scan leaked OnlyFans and Fansly content has become a common search term, reflecting both the demand for such material and the ongoing battle between content creators and those who seek to distribute their work without permission.
These platforms were designed to give creators more control over their content and provide a direct revenue stream, but they've also become targets for hackers and content thieves. The intimate nature of the content, combined with the financial investment required to access it, creates a perfect storm for unauthorized distribution.
The Broader Implications of Privacy Violations
Legal and Ethical Considerations
The leaking of private celebrity photos raises complex legal and ethical questions that society is still grappling with. While laws exist to protect against revenge porn and unauthorized distribution of intimate images, enforcement remains challenging in the borderless world of the internet.
Many countries have strengthened their laws regarding non-consensual sharing of intimate images, but the global nature of the internet means that content can be hosted in jurisdictions with different legal standards. This creates a patchwork of protections that can be difficult for victims to navigate.
The Role of Media and Public Consumption
The media's role in reporting on these leaks has evolved significantly over the years. While some outlets continue to publish or link to leaked content, many have adopted policies against distributing such material, recognizing the harm it causes to victims.
However, the public's appetite for celebrity gossip and scandal remains strong, creating a demand that drives the continued circulation of leaked content. This raises important questions about collective responsibility and the role that ordinary internet users play in perpetuating these violations through clicks, shares, and comments.
Protecting Yourself in the Digital Age
Best Practices for Digital Security
For both celebrities and ordinary individuals, protecting digital privacy requires vigilance and proactive measures. Strong, unique passwords for each online account, two-factor authentication, and careful management of cloud storage settings are essential first steps.
Regular security audits of online accounts and being cautious about what gets stored in the cloud can help minimize the risk of exposure. For those in the public eye, working with cybersecurity professionals to implement additional layers of protection is increasingly common.
The Future of Digital Privacy
As technology continues to evolve, so too will the methods used to protect and violate digital privacy. Emerging technologies like blockchain and decentralized storage systems offer potential solutions for giving individuals more control over their data, but they also present new challenges and vulnerabilities.
The conversation around digital privacy is likely to become even more complex as artificial intelligence and deepfake technology advance. The ability to create convincing fake content raises new questions about authenticity and the nature of privacy violations in an age where seeing is no longer believing.
Conclusion
The shocking leak of June 27th birthday secrets and nude photos serves as a stark reminder of the ongoing battle for digital privacy in our interconnected world. From major Hollywood stars to everyday individuals, no one is immune to the threat of having their most intimate moments exposed without consent.
As we've explored throughout this article, the consequences of these leaks extend far beyond the initial shock value, touching on complex issues of privacy, security, ethics, and the nature of celebrity in the digital age. While tools like Chiliradar offer some hope for monitoring and addressing unauthorized content distribution, the fundamental challenge of protecting digital privacy remains.
The path forward requires a collective effort from technology companies, lawmakers, media organizations, and individual internet users to create a digital environment that respects privacy and holds accountable those who violate it. Until then, the shocking leaks will continue, serving as painful reminders of the work still needed to protect our most private moments in an increasingly public world.
- What This Golden Retriever Chose For His Birthday Will Shock You
- Explosive New Epstein Israel Leak Nude Photos And Hidden Tapes Revealed

Hareem Shah Leak Shocking Video - Current Affairs Videos
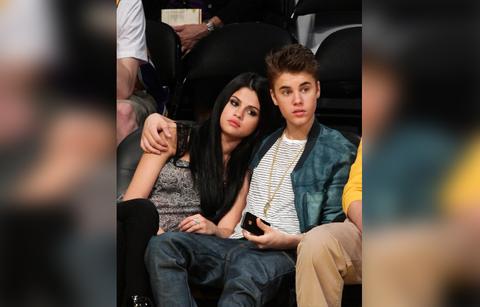
Selena Gomez Secrets & Scandals Exposed On 27th Birthday

Putin's Secret Blueprint for Ukraine Uncovered in Shocking Leak